With just under 50% of digital merchants reporting some kind of security breach, and online fraud growing at a faster rate than online sales, security is more important now than ever before. Gartner reports that by 2020 companies that are digitally trustworthy will generate 20% more online sales than those that are not.
Our model for delivering open and customizable software introduces a particular challenge. ZDNet found that 83.1% of Magento Commerce and Magento Open-source sites that reported hacks were running on outdated versions. While we emphasize security in every release, it is imperative that merchants keep their stores current to leverage those enhancements.
With these statistics and trends in mind, 2019 has been our year of security. Our engineers have been hard at work for the last 8 months making Magento Commerce 2 more secure by reducing our security issue backlog by over 93%. In Q2, we shipped 139 security fixes across all active Magento Commerce and Magento Open-source versions. In our upcoming Q3 release we'll ship a record number of 157 fixes! We’ve doubled our prior year’s investment in security and are changing our approach to security work by making broader strategic changes that improve M2 security posture across the board. We have a roadmap for more of these changes in 2020 as we continue our increased investment in security.
But wait, there's more! We listened to you at Magento Live, Imagine, and other events, and now we're making it easier to pick up security fixes. In Q3 we'll be shipping a security patch release for Magento Commerce and Open-source 2.3.2. The release will be called "2.3.2-p1". It will give you the option to get just the security fixes you need for Black Friday, but delay the less time-sensitive quality, performance, and other changes until later.
You might have noticed the unusual naming scheme for the security patch release, especially since it’s being released next to the 2.3.3 release. That's because the security patch will be based on the latest prior full patch release on our most recent release line to give you a possible upgrade path like this:
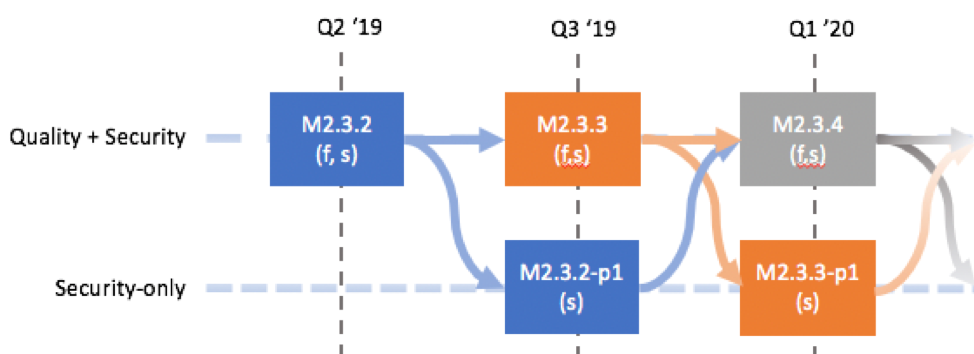
This flexible scheme gives you the familiar continuous path to functional and security fixes, or the option to take a lighter security patch release when you need to, which lets you remain secure for as long as six months before picking up a full release.
Edit 28 Sept 2020 - Please note the security releases also includes quality hot fixes since Magento has determined they are critical to run Magento effectively.
Here are a few examples to help illustrate your options:
Example 1 – A full upgrade:
- In Q3’19, you upgrade your 2.3.2 instance to 2.3.3.
- In Q1’20, you can upgrade your 2.3.3 instance to 2.3.4.
Example 2 – Security now, full service later:
- In Q3’19, you upgrade your 2.3.2 instance to 2.3.2-p1.
- In Q1’20, you can upgrade your 2.3.2-p1 instance to 2.3.4.
Example 3 – Security now, then the functional change you really need:
- In Q3’19, you upgrade your 2.3.2 instance to 2.3.2-p1.
- Between Q3’19 and Q1’20, you upgrade your 2.3.2-p1 instance to 2.3.3 to get access to the quality updates.
- In Q1’20, you upgrade your 2.3.3. instance to either 2.3.4 or 2.3.3-p1, depending on the complexity of the upgrade you want to take on.*
Example 4 – Security update to security update:
- In Q3’19, you upgrade your 2.3.2 instance to 2.3.2-p1.
- In Q1’20, you can upgrade your 2.3.2-p1 instance to 2.3.3-p1.**
Enough chit-chat! How can you get your hands on this security patch? We will release it in late September to our technology partners and Commerce customers as a Composer package.
We're committed to making our commerce products the most robust and secure choice out there, so give us your feedback. Let us know how we're doing and what you'd like to see more of.
*Note that you would be taking on an additional upgrade during this span.
**Note that we will do its best to support security patch release to security patch release configurations, but we will not fully validate this upgrade path as part of our patch release process.